KEIBIDROP
Encrypted peer-to-peer file sharing. Two devices connect directly and exchange files over an encrypted channel. Works over the internet or a local network. Open source.
Two Modes
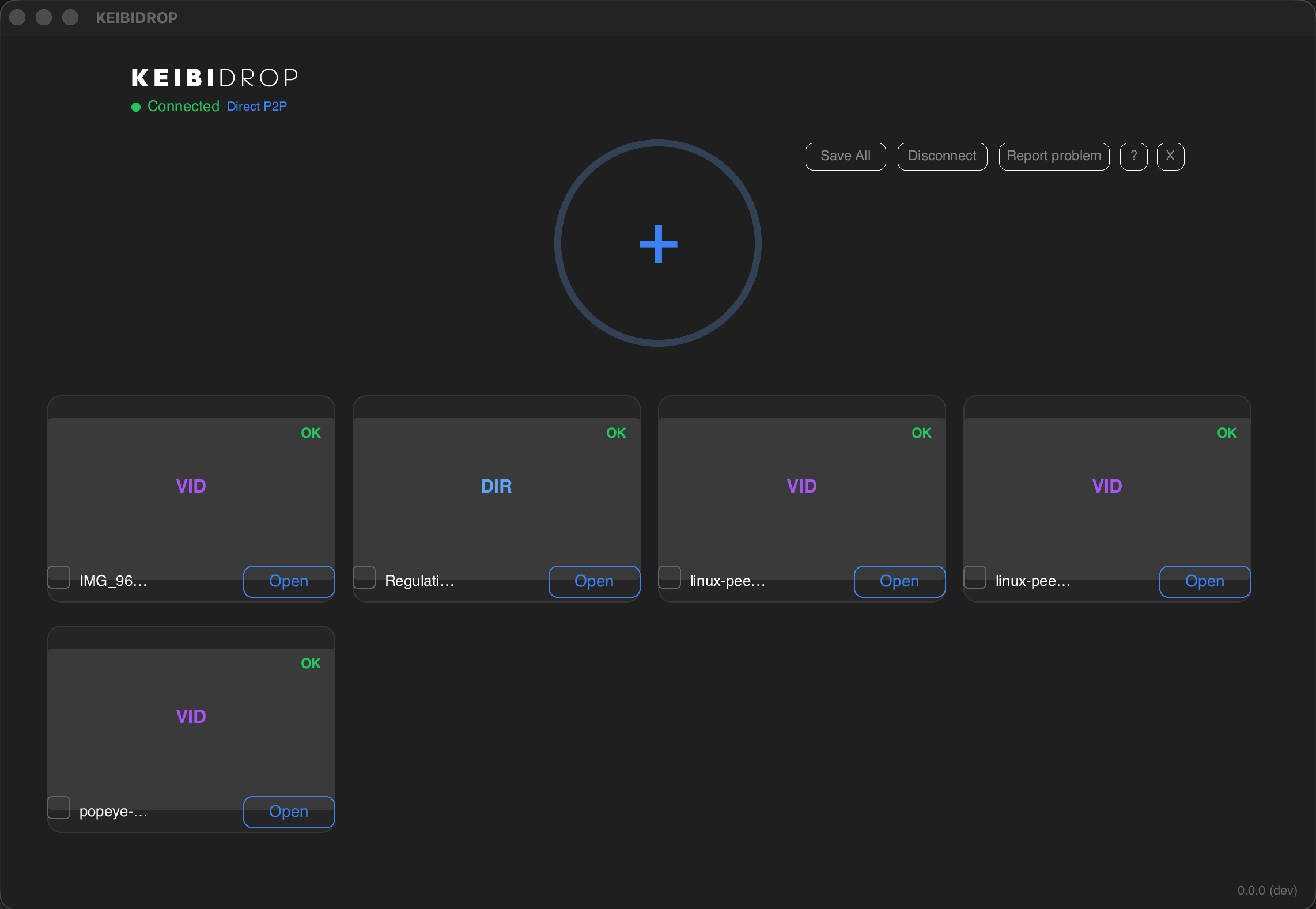
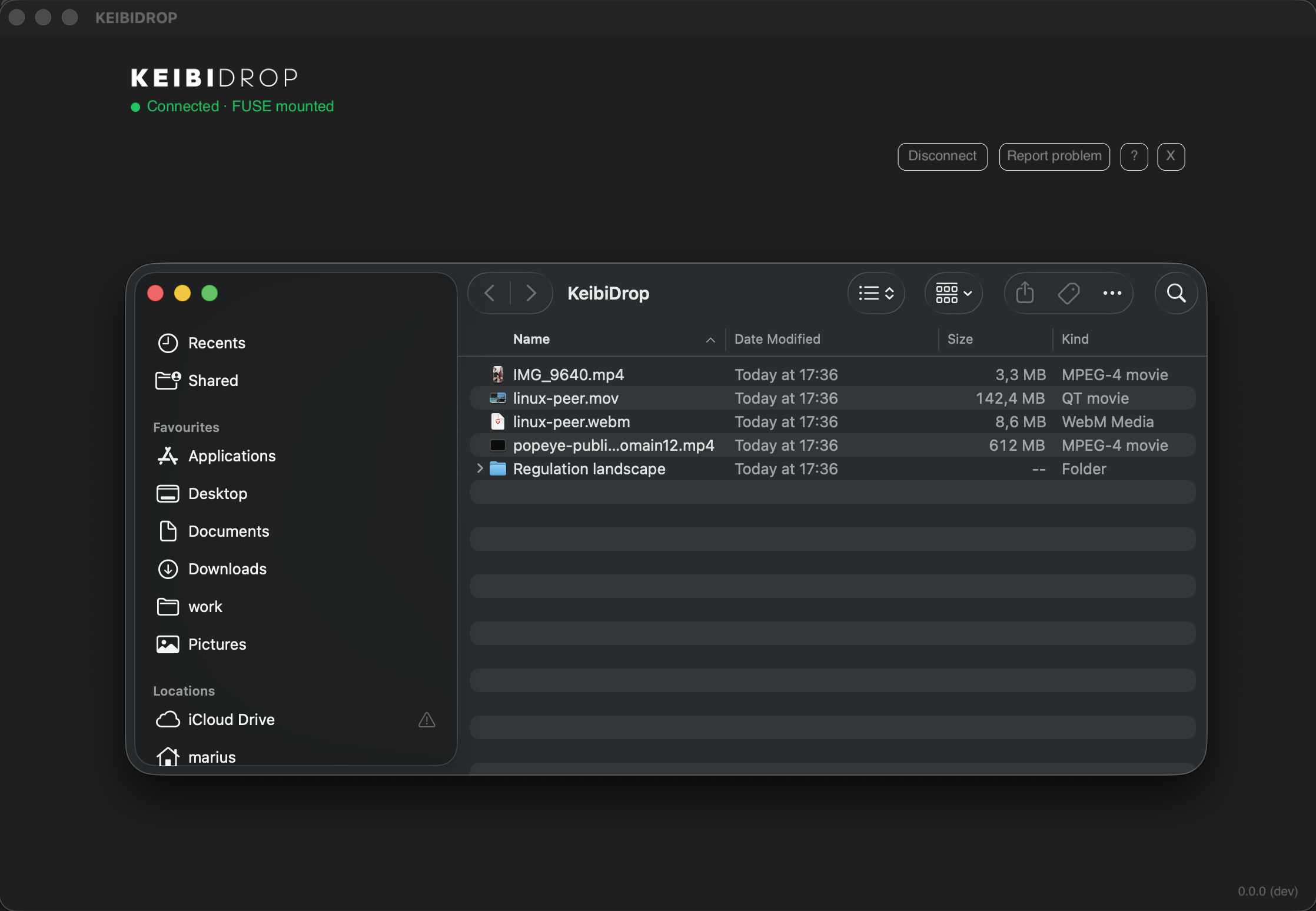
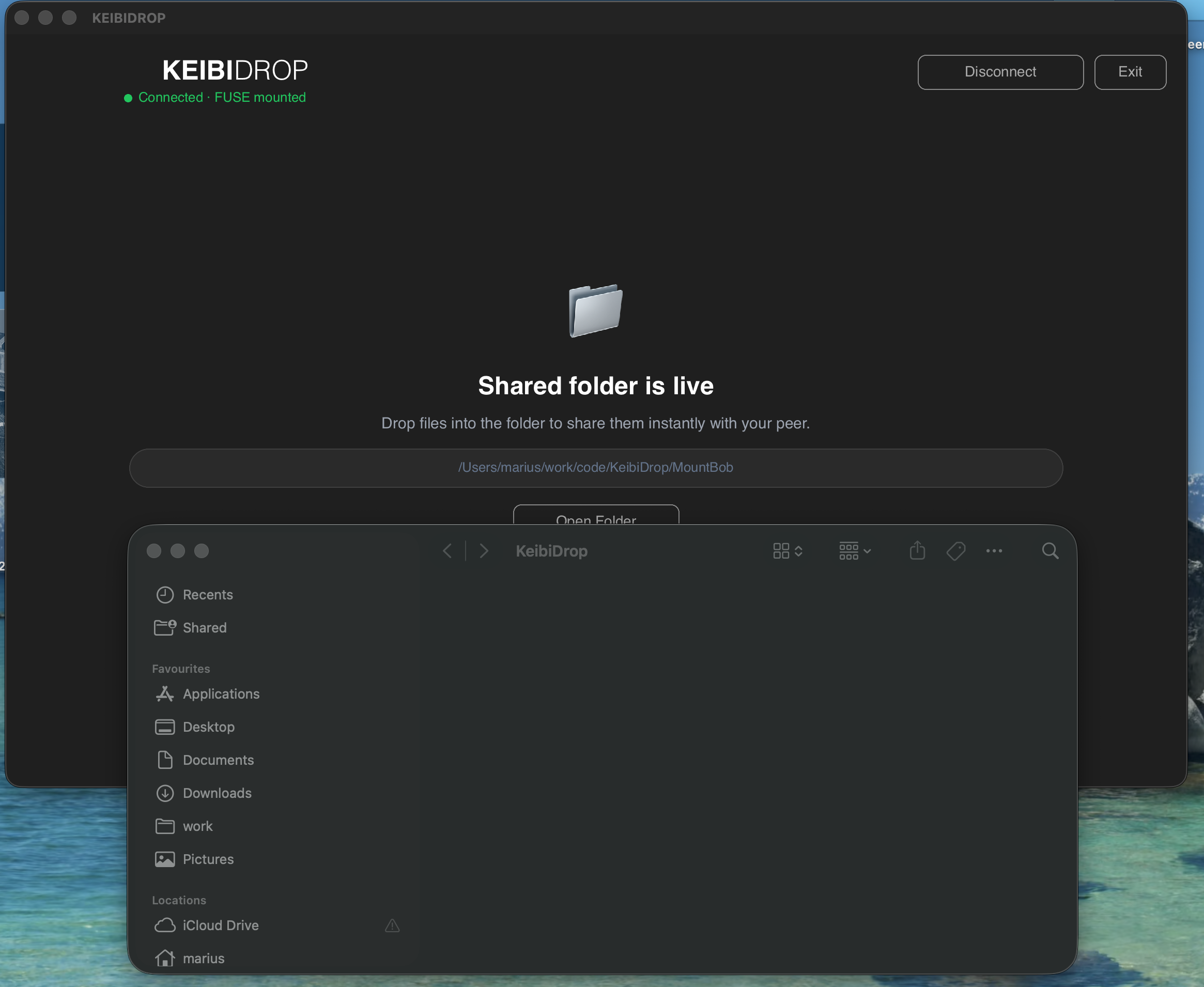
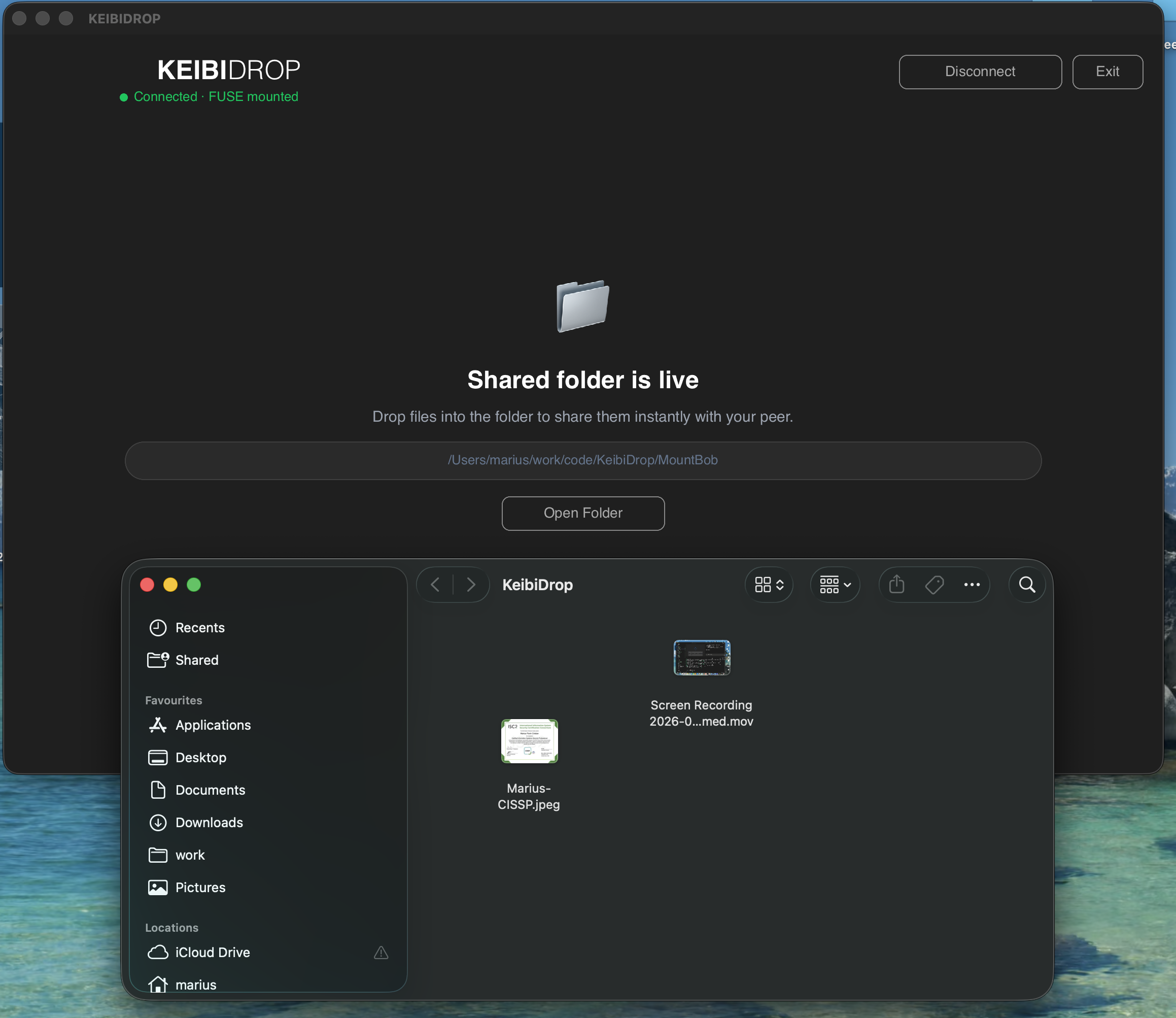
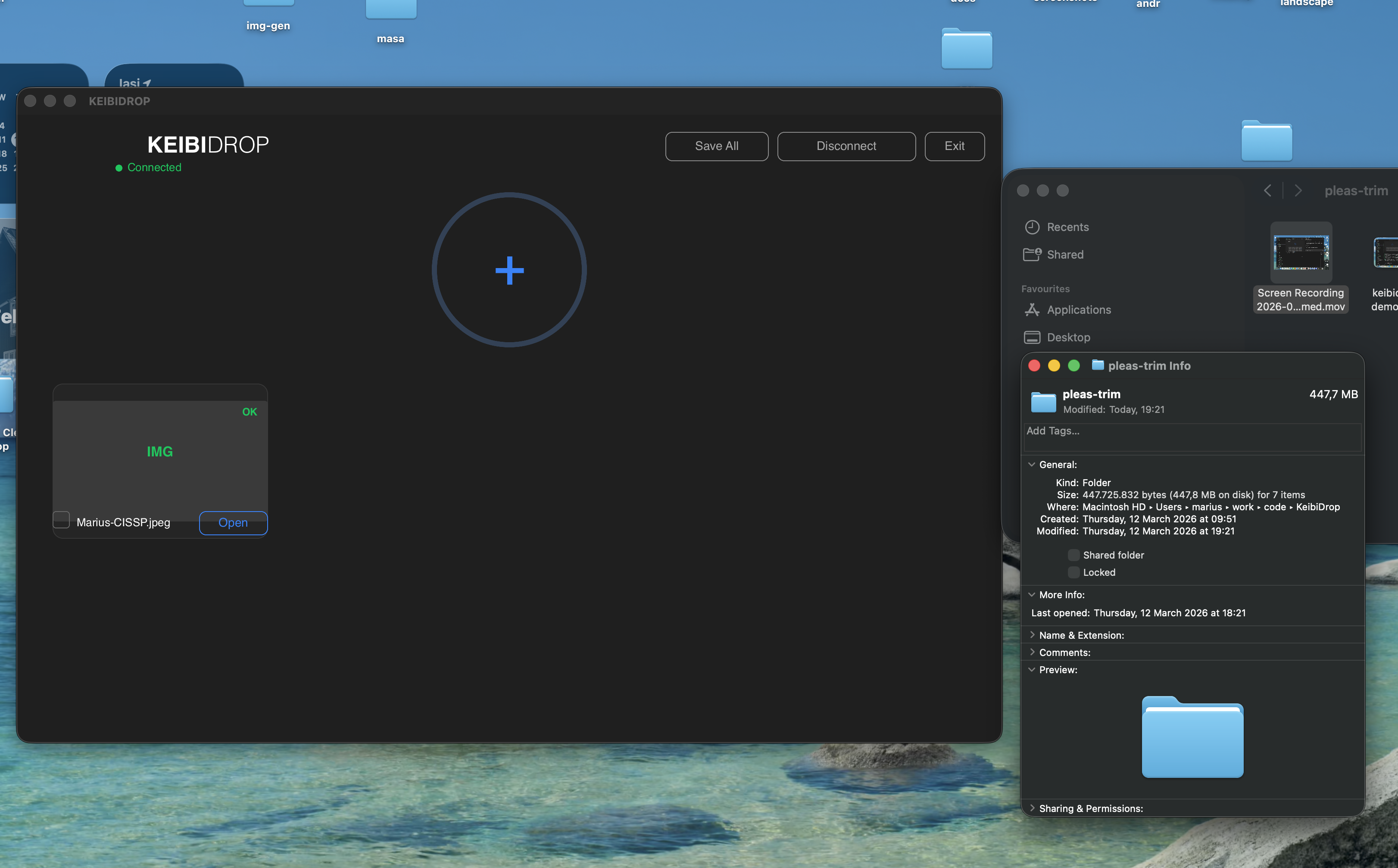
KEIBIDROP has two modes of operation. In direct transfer mode, you drag files into the app and your peer saves what they need. In virtual folder mode, your peer's files appear as a regular folder on your machine (via FUSE on macOS/Linux, WinFsp on Windows). Both modes are end-to-end encrypted.
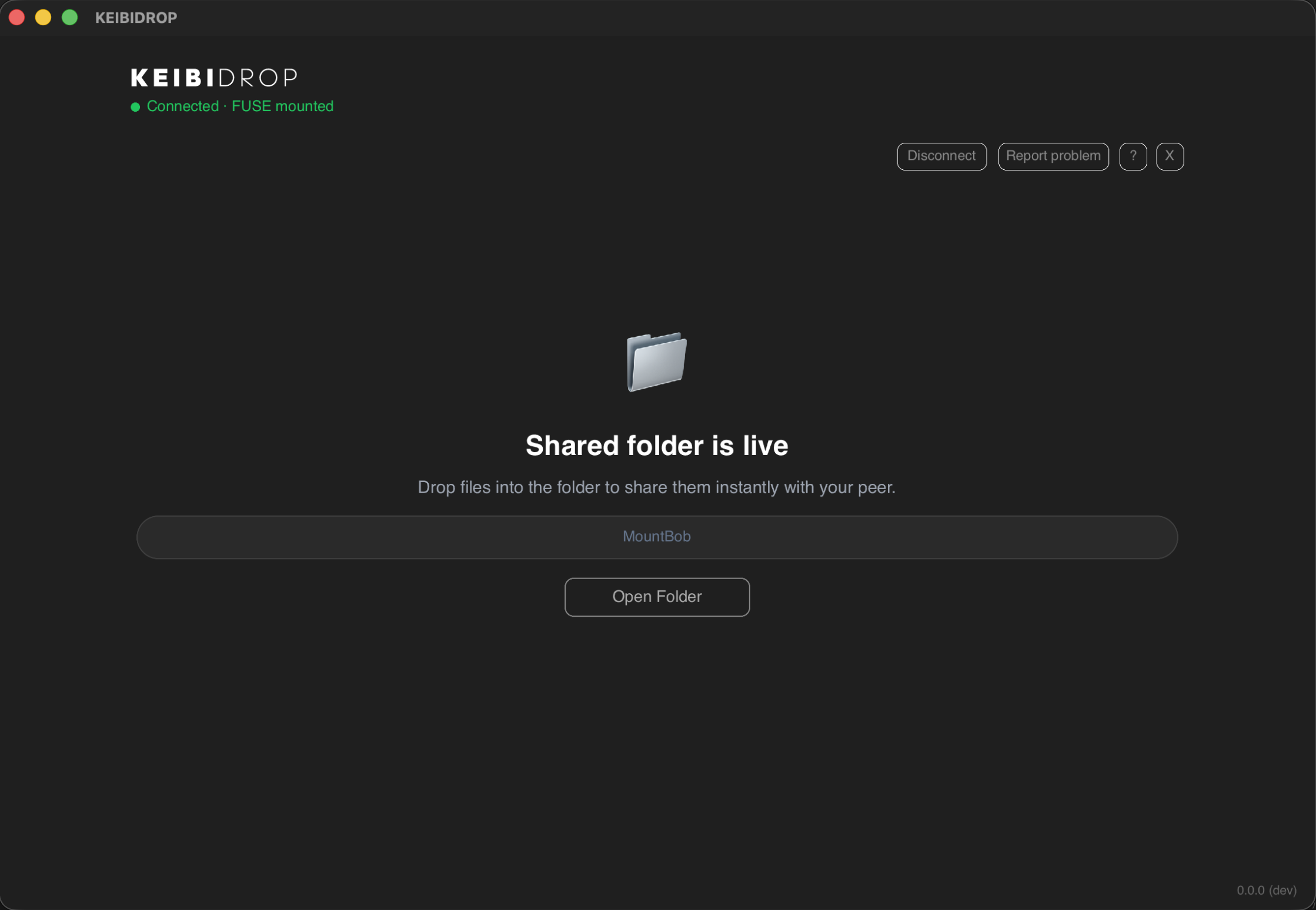
It Behaves Like a Real Folder
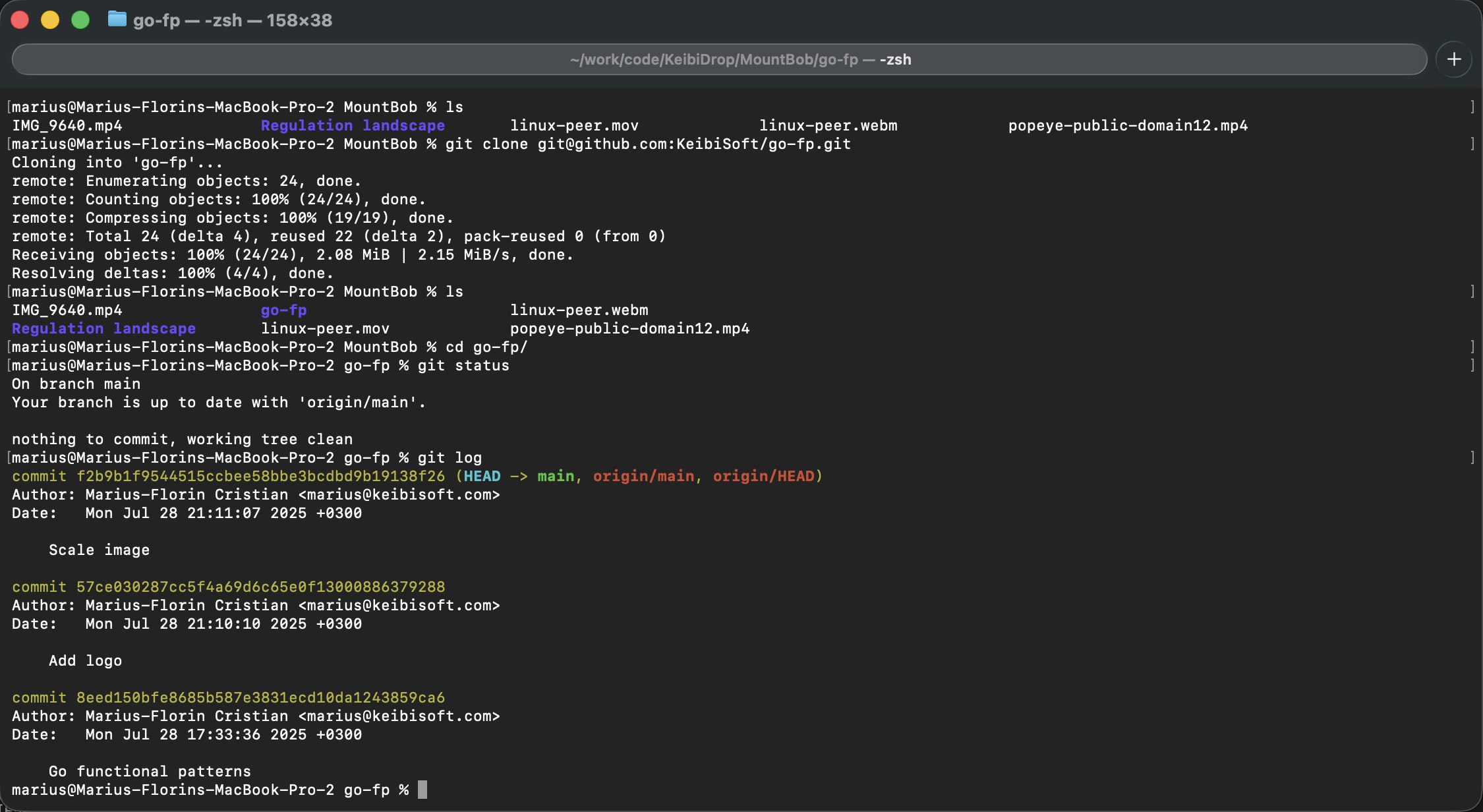
The virtual folder mount is a standard POSIX filesystem. Finder, Terminal, git, rsync, your IDE,
all work on it. You can git clone a repository into the shared folder and your peer
can run git log on their side.
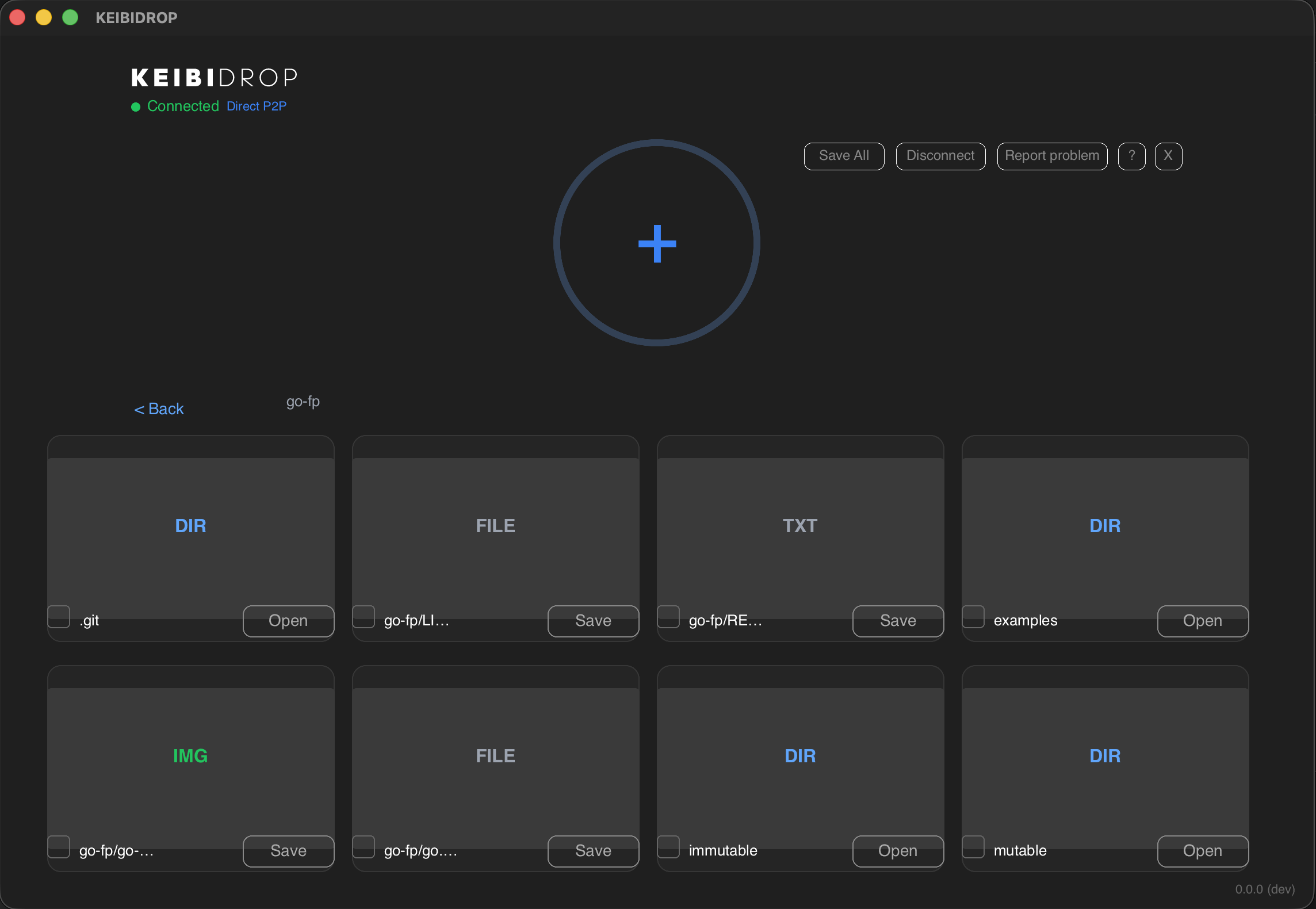
Browse Folders From Your Peer
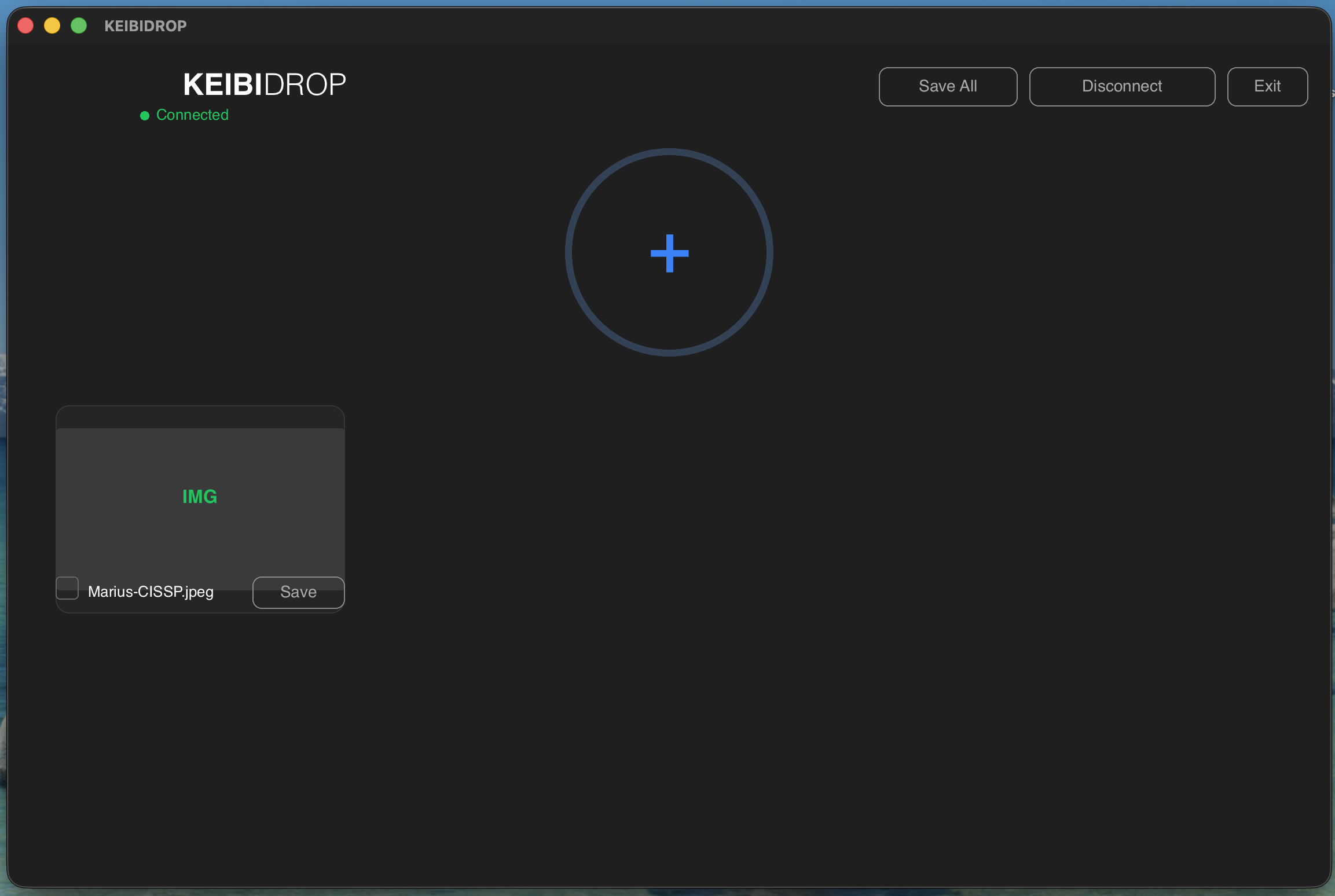
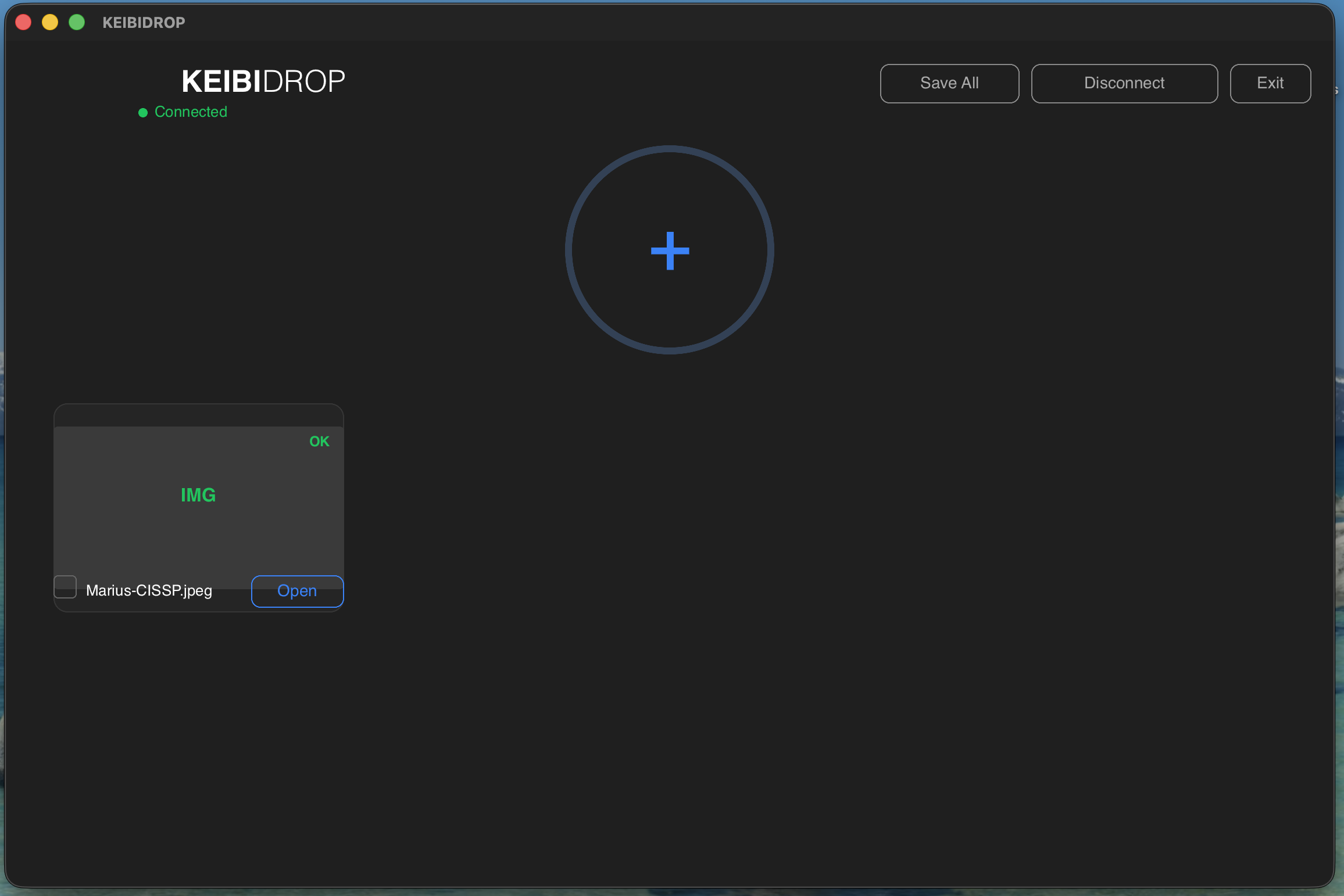
In direct transfer mode, directories sent by your peer show up as navigable folders. You can drill into them and save individual files or the entire directory.
What It Does
There is no upload limit. 5 KB config files and 500 GB database dumps both work. Transfers resume on reconnect.
ML-KEM-1024 + X25519 hybrid key exchange. AES-256-GCM or ChaCha20-Poly1305 for data. The relay cannot decrypt anything.
Files travel directly between devices. There is no upload-then-download step. On a local network, it saturates gigabit ethernet.
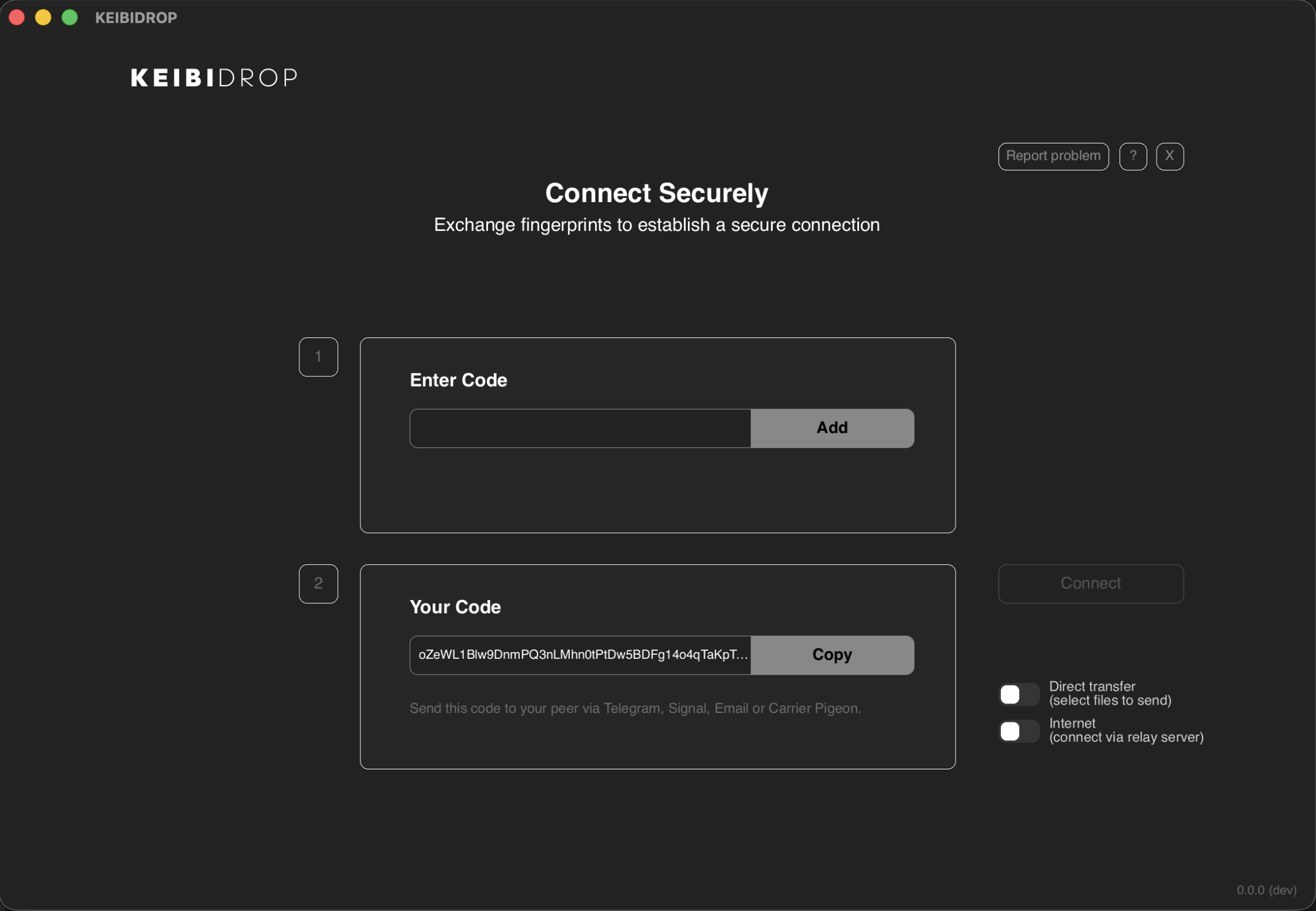
Open the app, exchange a code, connect. There are no accounts and no email verification.
On the same WiFi, devices discover each other via mDNS. Over the internet, they connect through an encrypted bridge relay.
A new cryptographic fingerprint is generated on each startup. Keys rotate on disconnect. Previous sessions cannot be linked to new ones.
Who Uses It
CLI and agent interfaces. Script it, automate it, embed it in CI. JSON output, Unix sockets, C FFI.
Post-quantum crypto, ephemeral keys, zero-knowledge relay. The code is auditable under MPL-2.0.
Legal documents, source code, medical records. Transfer sensitive files without trusting a third party.
Send photos, videos, project folders to a friend. Open the app, exchange codes, drag files in.
*A signaling relay exchanges ephemeral public keys so peers can find each other. When peers cannot connect directly, a bridge relay forwards encrypted traffic between them. Neither relay can read the data: all traffic is encrypted end-to-end with keys derived from the fingerprint exchange.
How It Works
-
Start KEIBIDROP on both devices
Each device generates a unique cryptographic fingerprint. This is your identity for the session.
-
Exchange codes
Copy your code and send it to your peer over Signal, email, a sticky note. They paste yours, you paste theirs.
-
Connect
One peer creates a room, the other joins. On LAN, toggle local mode and skip codes entirely. The post-quantum handshake completes in under 3ms.
-
Share files
Drag files into the window, use the CLI, or open the virtual folder. Files appear on the other side in real time.
More Screenshots
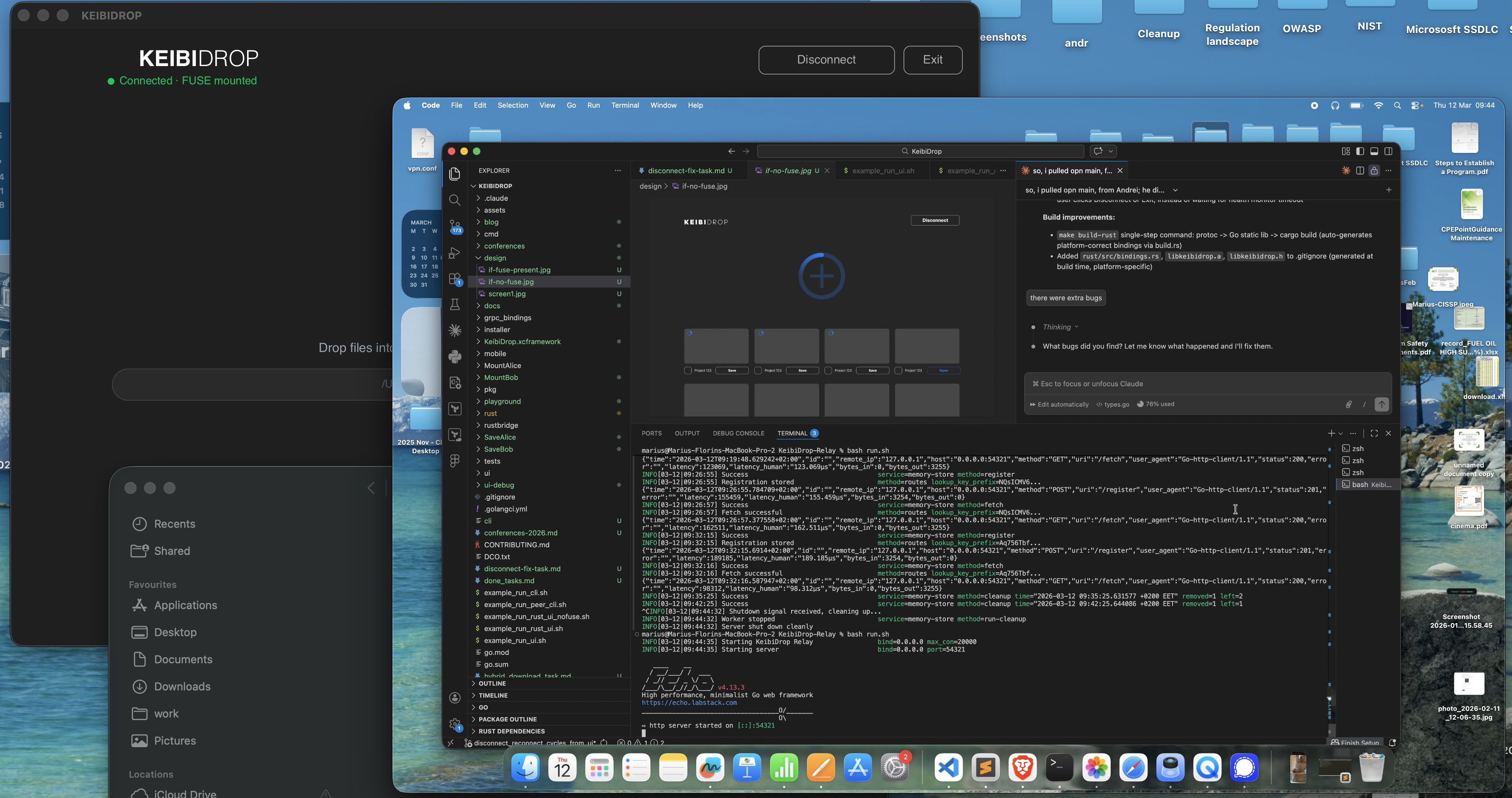
FUSE mode: shared files as a virtual folder
Direct transfer mode: drag, drop, save
Three Interfaces
Rust + Slint native UI. Drag and drop, progress bars, file type icons. macOS, Linux, Windows.
Terminal REPL with a prompt. Type commands, see results. For people who live in the terminal.
Non-interactive daemon with JSON output over Unix socket. Built for AI agents and automation scripts.
Interactive CLI
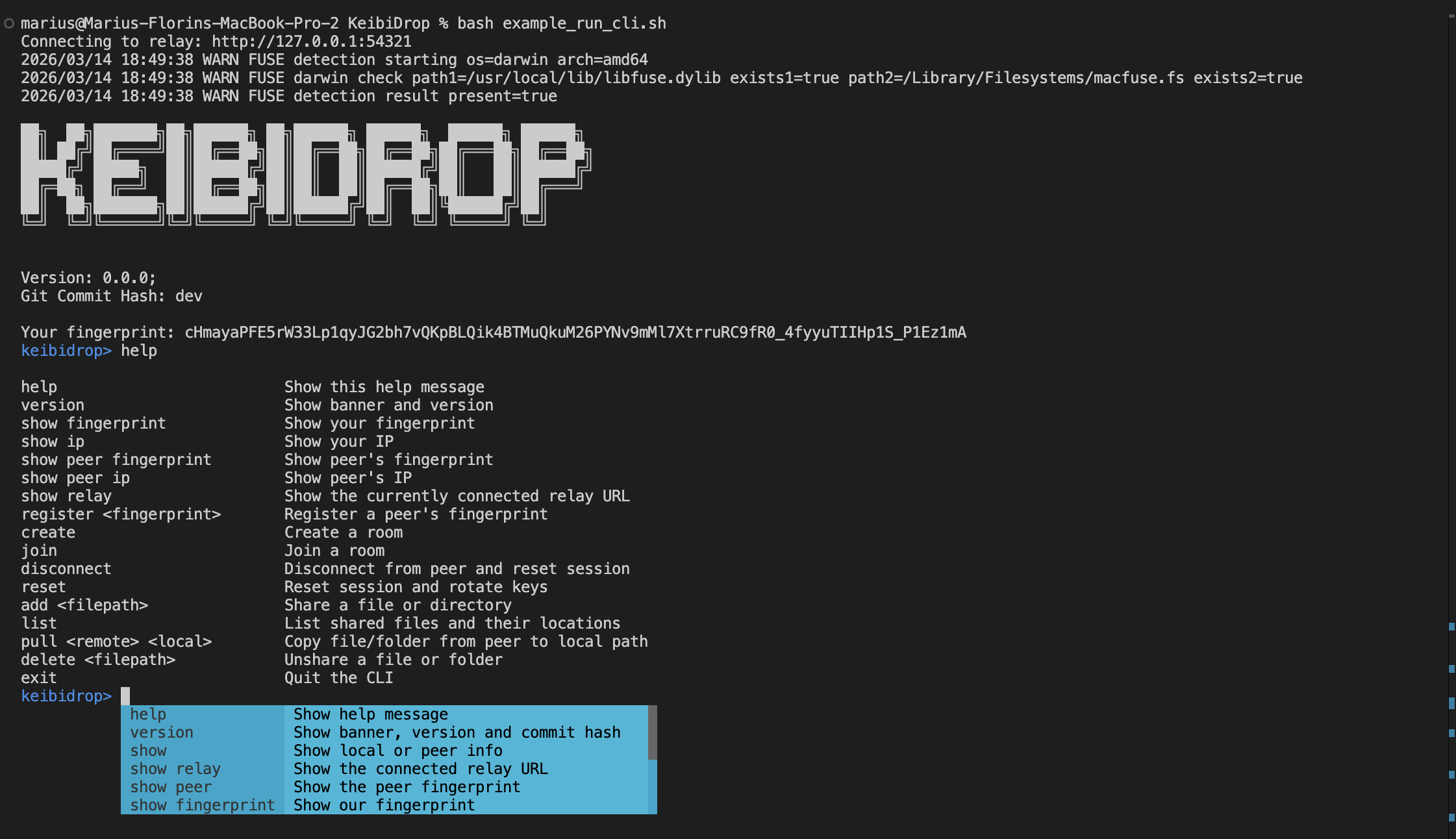
All three interfaces support FUSE (virtual folder) and direct transfer (explicit add/pull commands).
Under The Hood
Built with
- Go 1.24 for backend, networking, cryptography, FUSE. Standard library
crypto/mlkemfor post-quantum. - Rust + Slint for the native desktop UI. 20 MB binary.
- gRPC + Protocol Buffers for type-safe peer communication.
- cgofuse for cross-platform FUSE bindings (macOS, Linux, Windows).
~11,000 lines of Go, ~5,000 lines of tests.
Privacy
KEIBIDROP sends no analytics, no crash reports, no usage data. Identity is a cryptographic key pair generated locally. Keys rotate on every disconnect; your fingerprint changes and previous sessions cannot be linked to new ones.
The signaling relay exchanges ephemeral public keys between peers. It stores encrypted blobs it cannot decrypt, indexed by a lookup token derived from the fingerprint (not the fingerprint itself). It cannot correlate registrations. When direct connection is not possible, a bridge relay forwards encrypted traffic using outbound connections from both peers. The bridge cannot decrypt the data.
Session keys are rekeyed automatically after 1 GB of data or 1 million messages. If a key is compromised, only a fraction of the session is exposed. The full codebase is auditable under MPL-2.0.
Get Started
Interactive CLI
# Terminal 1 (Alice) export KEIBIDROP_RELAY=https://keibidroprelay.keibisoft.com export TO_SAVE_PATH=./SaveAlice TO_MOUNT_PATH=./MountAlice ./keibidrop-cli keibidrop> register <Bob's fingerprint> keibidrop> create keibidrop> add /path/to/file.pdf
# Terminal 2 (Bob) export KEIBIDROP_RELAY=https://keibidroprelay.keibisoft.com export TO_SAVE_PATH=./SaveBob TO_MOUNT_PATH=./MountBob ./keibidrop-cli keibidrop> register <Alice's fingerprint> keibidrop> join keibidrop> list keibidrop> pull file.pdf ./SaveBob/file.pdf
Agent CLI (kd)
The kd tool runs as a background daemon. All commands return JSON.
Designed for AI agents (Claude Code, etc.) and automation scripts.
# Start daemon (FUSE mode recommended for agents) KD_SAVE_PATH=./saved KD_MOUNT_PATH=./mount \ KD_SOCKET=/tmp/kd.sock ./kd start # Exchange fingerprints and connect ./kd show fingerprint ./kd register <peer-fp> ./kd create # After connecting, the mount path is a live synced folder ls ./mount/ cat ./mount/readme.txt cp ./myfile.pdf ./mount/ # Cleanup ./kd disconnect ./kd stop
Full reference: Agent Integration Guide
Desktop GUI (Rust + Slint)
export NO_FUSE=1 # omit for FUSE mode export TO_SAVE_PATH=./SaveAlice TO_MOUNT_PATH=./MountAlice ./keibidrop-rust
FFI (embed in your app)
KEIBIDROP compiles to a C static library (libkeibidrop.a + libkeibidrop.h).
Call from Rust, Swift, Python, or any language with C FFI.
KD_Initialize(relay, inbound, outbound, mount, save, fuse, prefetch, push);
KD_AddPeerFingerprint(peer_fp);
KD_CreateRoom();
KD_AddFile("/path/to/file.pdf");
KD_SaveFileByName("file.pdf", "/save/path/file.pdf");
The KEIBIDROP Blog Series
-
Building Post-Quantum Encrypted File Sync
Full technical overview. Architecture, crypto choices, FUSE challenges, lessons learned.
-
Debugging FUSE Deadlocks on Intel Macs
Lock ordering and brief-lock patterns that saved us from frozen filesystems.
-
Hybrid Post-Quantum Encryption for gRPC
ML-KEM + X25519 handshake. Custom transport credentials. 3ms overhead.
-
Privacy-Preserving P2P Discovery
Dual key derivation, encrypted registration blobs, and why the relay sees nothing.
-
Forward Secrecy: Automatic Key Rotation
Rekey after 1 GB or 1M messages. Counter-based nonces. Hybrid ML-KEM + X25519 rekey.
-
Building a CLI for AI Agents
The kd tool: daemon + Unix socket, JSON output, direct function calls.
-
Testing P2P Systems Without External Dependencies
Mock relay, TestPair harness, dynamic ports, 36 tests in 139 seconds.
-
Cross-Platform File Sync
macOS atomic saves, Windows file locking, Linux FUSE versions.
-
Building KEIBIDROP While Burned Out
519 commits, 10 months, two developers. Building during recovery.
-
The Write/Release Race Condition
When the kernel closes your file mid-write. Timestamp debugging and RWMutex.
-
10x FUSE Performance via Block Size Tuning
One line change: st_blksize 4KB to 2MB. 300 MB/s to 3,400 MB/s.
-
Making Git Work Inside a FUSE Filesystem
mmap, fsync races, fcopyfile quirks, per-file direct_io.
-
Why macOS Preview Can't Read Your FUSE Files
Three-layer debugging: sandboxing + Gatekeeper + mmap.
-
Making Git Clone Work Between Peers
Rename races, debounce, prefetch semaphores, negative vnode caching.
-
Optimizing Encrypted Transfer Speed
AEAD caching, combined writes, async cache, push-based streaming.
-
SecureConn Performance
Profiling the encrypted transport layer. Where the cycles go.
-
AES-GCM Hardware Acceleration
AES-NI, ARM crypto extensions, and measured throughput.
-
Benchmarks vs the Competition
KeibiDrop vs croc vs magic-wormhole vs LocalSend. Measured numbers.
-
The File Descriptor Reuse Race
POSIX fd recycling caused 50% data corruption. Opaque handle IDs fixed it.
-
Running PostgreSQL Over FUSE
Can you run a database on a peer-to-peer virtual filesystem? Benchmark results.
-
Cross-Peer PostgreSQL Migration
Migrating a live PostgreSQL instance from Linux to Mac over an encrypted bridge.
-
v0.1.0 Release
First public release. What shipped and what's next.
Open Source
KEIBIDROP is free and open source under the Mozilla Public License 2.0. The source code is available for inspection, cryptographic audit, and building from source.
Commercial licensing, priority support, custom integrations, and private relay hosting available for organizations.